-

Brett Kavanaugh's Failure to Acknowledge the Changes in Communications Technology: The Implications for Privacy
Facebook became available to the general public in 2006; Apple's smartphone was announced the following year. In little over a decade, the devices, and the communications they engender, have become ubiqu... -

Sound Recommendations on Digital Evidence and Law Enforcement
Professor Jennifer Daskal and Will Carter of the Center for Strategic and International Studies have written a terrific report, “Low- -

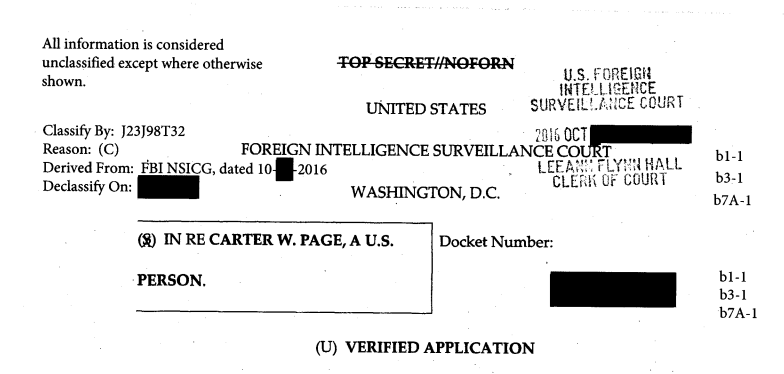
What to Make of the Carter Page FISA Applications
The release of the Carter Page FISA applications represents a monumental disclosure to the public—and underlines just how disingenuous House intelligence committee Chairman Devin Nunes has been. -

A Deeper Look at Deepfakes: Our New Article and an Event at Heritage on Thursday
Back in February, we joined forces in this post to draw attention to the wide array of dangers to individuals and to society posed by advances in “deepfake” technology (that is, the capacity to alter aud... -

Document: Justice Department Says FISA Court Lacks Jurisdiction to Hear Private Records Requests
The Justice Department filed a brief with the Foreign Intelligence Surveillance Court on behalf of the United States arguing that the court lacks the jurisdiction to hear cases from private parties reque... -

Why the U.S. Needs Federal Data Privacy Legislation
“I Love Lucy” provides the central metaphor for a Brookings paper released today on what to do to protect privacy. It comes from the episode where Lucy goes to work wrapping candies on an assembly line. ... -

Cloud Act Implementation Issues
Congress passed the Cloud Act as part of an omnibus spending bill in March over the objection of many civil society groups, including the Center for Democracy & Technology (with which I am affiliated). T... -

The NSA and the USA Freedom Act
The National Security Agency has announced a startling failure in the implementation of the USA Freedom Act of 2015. According to a public statement released by NSA on June 28, the call detail records th... -

Document: Lawsuit Argues FOSTA is Unconstitutional
The Electronic Frontier Foundation has filed a lawsuit challenging the constitutionality of FOSTA. -

How Congress Can De-Escalate the Second Crypto War: Fund Research and Broker a Crypto Armistice
There’s been a flurry of encryption news over the past few months. In February, the National Academies released a report that discussed early-stage research into the design of secure cryptographic system... -

The Fifth Anniversary of the Snowden Disclosures
When reading about Snowden, keep in mind the dedicated NSA employees who strive to uphold the rule of law and protect their country. -

Corporate Data Collection and U.S. National Security: Expanding the Conversation in an Era of Nation State Cyber Aggression
This post has been adapted from prepared remarks delivered at the Georgetown Law Cybersecurity Law Institute luncheon on May 24, 2018.
The upcoming main navigation can be gotten through utilizing the tab key. Any buttons that open a sub navigation can be triggered by the space or enter key.